In 1983, the film WarGames imagined a teenager who accidentally accessed a Pentagon computer system and triggered a simulation program, subsequently interpreted as the prelude to a nuclear war. The film made such an impression on Ronald Reagan that he asked his advisers whether such an intrusion into America’s most sensitive systems was possible. A week later, the answer came: “Mr. President, the problem is far worse than you think.”
Nuclear weapons policies are based on a series of bets, often far-reaching, on the future of nuclear deterrence. First, nuclear-armed countries gamble that the fear of retaliation will always be enough to prevent an adversary from striking first, and that they will always have the expertise and luck necessary to prevent accidental explosions. They bet that possessing nuclear weapons will remain a source of security rather than insecurity in decades to come.
However, as my colleagues Sterre van Buuren and Benoît Pelopidas and myself demonstrate, there are several plausible future scenarios in which possessing nuclear weapons will generate more real costs than potential benefits in a world that has warmed by several degrees. Maintaining a credible and safe arsenal will require budgetary choices at the expense of other urgent spending made necessary by the climate crisis.
The universe of existential risks that could justify the use of nuclear weapons may also be expanding. For example, experts worry that water shortages in Pakistan and India could become fertile ground for a conflict leading to nuclear escalation.
But there is another, more implicit bet involved here: that nuclear arsenals, which are complex, highly digitalised technological systems, offer no cyber vulnerabilities that could be exploited by an actor seeking to disrupt their normal functioning.
The recent breakthrough of Anthropic’s latest AI model Claude Mythos reveals just how much the conditions of that bet could change in the long term.
Mythos and the future of cybersecurity
“Mythos” was launched on April 7 2026 by the public benefit corporation Anthropic – which markets the Claude series of large language models (LLMs). This model, which has not been commercially released but made available to a restricted working group composed of around a dozen major American tech giants (Google, Microsoft, Apple, NVIDIA, Amazon Web Services, etc.), reportedly achieves an unprecedented success rate in detecting vulnerabilities in computer systems.
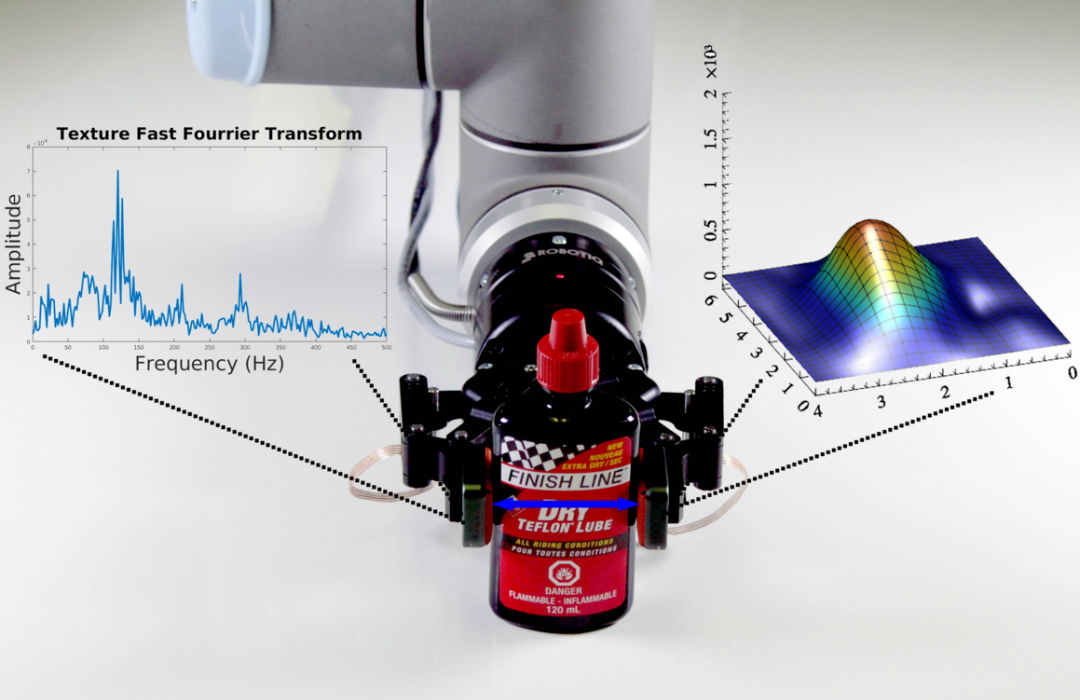
Mythos reportedly succeeded in detecting “zero-day” vulnerabilities in various web browsers, software, and operating systems with an impressive success rate.
A “zero-day” vulnerability is a critical security flaw in an information system for which no protection yet exists, making attacks possible with effectively “zero days” available to respond. According to Anthropic, Mythos managed to develop methods for exploiting these vulnerabilities in record time – likely in less than a day – with a success rate of 72.4%.
Although this information comes from the company itself – which has every incentive to exaggerate its results – some public evidence has been provided.
Sylvestre Ledru, Mozilla’s engineering director responsible for the Firefox browser, stated that Mythos helped uncover an “absolutely staggering” number of vulnerabilities in their software. For example, a nearly twenty-seven-year-old security flaw which had survived numerous audits was discovered in an open-source operating system widely used by cybersecurity services, OpenBSD.
Mythos sheds light on a larger phenomenon: that the increase in offensive capabilities – not only among states but also private actors such as cybercriminals – in the cyberspace could be accelerated by AI development, while uncertainty is emerging about whether defensive actors can react quickly enough to patch existing vulnerabilities.
Even if Mythos does not fully live up to the announced performance levels, the development of LLMs since the early 2020s has shown how rapidly their capabilities improve. We are therefore facing an acceleration in the development of offensive capabilities and their diffusion to a broader range of actors. This means a potentially rising probability of successful cyberattacks, as well as an increase in their absolute number.
The vulnerability of nuclear arsenals
To understand the vulnerability of nuclear weapons to cyberattacks, one must remember that a “nuclear arsenal” means far more than a stockpile of warheads. The normal operation of modern nuclear arsenals depends on a vast configuration of technologies: nuclear warheads, the missiles capable of delivering them, communication technologies ensuring that orders are transmitted from the President to the operator responsible for launching the weapons, as well as early warning systems designed to monitor the skies for signs of a potential enemy nuclear strike. These elements must communicate with one another to ensure control over the weapons.
And there are more of those than one might think. As Herbert Lin, a Stanford University researcher and author of a study on cyber threats and nuclear weapons, notes, the “nuclear button” metaphor is oversimplified: once the president presses it, a whole series of “cyber-buttons” must also be pressed to trigger and manage nuclear operations – each representing another point where cyberattacks could interfere, for example by preventing critical information from arriving.
The President might not receive enough information – or any at all – to determine that an attack is underway. Or he might be unable to communicate launch orders to submarine forces. Worse still, the nightmare scenario imagined since the 1950s could occur: a false launch order could be transmitted to missile operators.
The scenarios do not even need to be that extreme: the order might be transmitted with delays, or not transmitted to all forces, resulting in weaker retaliation than intended. The retaliation itself might be blocked: in 2010, an American command center lost communication with around fifty nuclear missiles for nearly an hour. An adversary could exploit such weaknesses.
Alternatively, a large-scale cyberattack carried out by non-state actors could create the impression that an adversary is targeting our nuclear arsenal, creating a risk of inadvertent escalation. Similarly, an attack on command-and-control systems related to conventional operations could be interpreted as endangering a state’s nuclear arsenal if those systems happened to be integrated.
One can also imagine cyber operations targeting the weapons themselves – the hardware rather than the software of the arsenal. Of course, nuclear security actors are not simply waiting for attacks to happen. They continuously develop and test defensive capabilities. The problem is that the complexity of existing systems makes it impossible to state with certainty that no vulnerabilities exist.
As James Gosler, formerly in charge of the security of American nuclear systems at Sandia National Laboratories, explains, beginning in the 1980s, the exponential increase in the complexity of components inside nuclear weapons meant that:
“you could no longer make the statement that any of these micro-controlled systems [used to ensure the functioning of the detonation mechanism] were vulnerability-free.”
That does not mean vulnerabilities necessarily exist. But it does mean that no actor can know for certain whether they do. So, should we fear that nuclear arsenals could one day be “hacked”?
In truth, we do not know. Such scenarios are possible: no large, complex information system can be guaranteed with total certainty to be completely reliable. The evolution of cyberattack tools, and their potential diffusion among a wide range of state and non-state actors, makes this kind of future scenario potentially more likely and, in any case, plausible.
A new bet on the future
Mythos highlights a new dimension to the nuclear gamble, born from the development of new technologies and their integration into nuclear arsenals.
First, we are betting on the absence of vulnerabilities within these systems – even though it is impossible to measure that probability with certainty. It changes over time as systems are updated, replaced, and connected to others. If vulnerabilities nevertheless exist, we then bet that advances in offensive cyber capabilities will always be matched, and matched in time, by advances in defensive capabilities – even in the age of artificial intelligence. Once again, that probability cannot be determined, because defensive capability development is often reactive: it depends on our knowledge of offensive capabilities and existing vulnerabilities, both of which are inherently uncertain.
We are therefore betting that our defences against cyberattacks – and those of other nuclear-armed states – will be enough. Otherwise, we are betting that luck will remain on our side and that existing vulnerabilities will not be discovered – like the one that existed for 27 years in OpenBSD’s code. It is a gamble on luck because, in this scenario, what saves us is the adversary’s inability or unwillingness, over which we have no control, to develop effective capabilities.
The ability of existing control practices to fulfil their role has become more uncertain with the arrival of large AI models capable of detecting vulnerabilities and designing cyberattacks on a massive and automated scale. Choosing a security policy based on nuclear weapons therefore amounts to betting that, in the future just as in the past, luck will always remain on our side.
The post “Hacking the bomb? What Claude Mythos AI reveals about the gamble of nuclear deterrence” by Thomas Fraise, Postdoctoral research fellow, University of Copenhagen; Sciences Po was published on 05/12/2026 by theconversation.com